Picture: Shutterstock.
Apple and the satellite-based broadband service Starlink every not too long ago took steps to handle new analysis into the potential safety and privateness implications of how their companies geo-locate units. Researchers from the College of Maryland say they relied on publicly obtainable information from Apple to trace the placement of billions of units globally — together with non-Apple units like Starlink programs — and located they may use this information to observe the destruction of Gaza, in addition to the actions and in lots of instances identities of Russian and Ukrainian troops.
At challenge is the best way that Apple collects and publicly shares details about the exact location of all Wi-Fi entry factors seen by its units. Apple collects this location information to offer Apple units a crowdsourced, low-power different to consistently requesting world positioning system (GPS) coordinates.
Each Apple and Google function their very own Wi-Fi-based Positioning Programs (WPS) that receive sure {hardware} identifiers from all wi-fi entry factors that come inside vary of their cellular units. Each report the Media Entry Management (MAC) tackle {that a} Wi-FI entry level makes use of, often known as a Primary Service Set Identifier or BSSID.
Periodically, Apple and Google cellular units will ahead their places — by querying GPS and/or by utilizing mobile towers as landmarks — together with any close by BSSIDs. This mix of knowledge permits Apple and Google units to determine the place they’re inside a couple of toes or meters, and it’s what permits your cell phone to proceed displaying your deliberate route even when the gadget can’t get a repair on GPS.
With Google’s WPS, a wi-fi gadget submits a listing of close by Wi-Fi entry level BSSIDs and their sign strengths — by way of an software programming interface (API) request to Google — whose WPS responds with the gadget’s computed place. Google’s WPS requires a minimum of two BSSIDs to calculate a tool’s approximate place.
Apple’s WPS additionally accepts a listing of close by BSSIDs, however as a substitute of computing the gadget’s location based mostly off the set of noticed entry factors and their obtained sign strengths after which reporting that consequence to the consumer, Apple’s API will return the geolocations of as much as 400 hundred extra BSSIDs which can be close by the one requested. It then makes use of roughly eight of these BSSIDs to work out the consumer’s location based mostly on identified landmarks.
In essence, Google’s WPS computes the consumer’s location and shares it with the gadget. Apple’s WPS offers its units a big sufficient quantity of knowledge concerning the location of identified entry factors within the space that the units can try this estimation on their very own.
That’s in keeping with two researchers on the College of Maryland, who theorized they may use the verbosity of Apple’s API to map the motion of particular person units into and out of just about any outlined space of the world. The UMD pair mentioned they spent a month early of their analysis repeatedly querying the API, asking it for the placement of greater than a billion BSSIDs generated at random.
They realized that whereas solely about three million of these randomly generated BSSIDs had been identified to Apple’s Wi-Fi geolocation API, Apple additionally returned an extra 488 million BSSID places already saved in its WPS from different lookups.
UMD Affiliate Professor David Levin and Ph.D scholar Erik Rye discovered they may largely keep away from requesting unallocated BSSIDs by consulting the record of BSSID ranges assigned to particular gadget producers. That record is maintained by the Institute of Electrical and Electronics Engineers (IEEE), which can be sponsoring the privateness and safety convention the place Rye is slated to current the UMD analysis later at the moment.
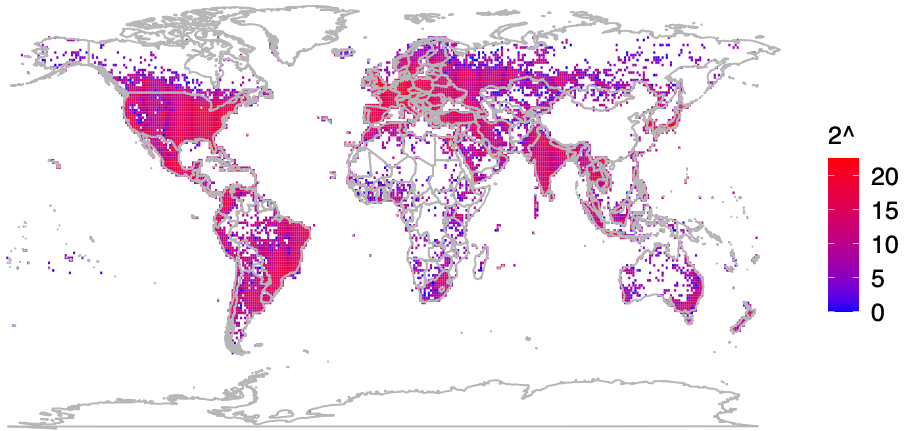
Plotting the places returned by Apple’s WPS between November 2022 and November 2023, Levin and Rye noticed that they had a close to world view of the places tied to greater than two billion Wi-Fi entry factors. The map confirmed geolocated entry factors in practically each nook of the globe, other than virtually the whole lot of China, huge stretches of desert wilderness in central Australia and Africa, and deep within the rainforests of South America.
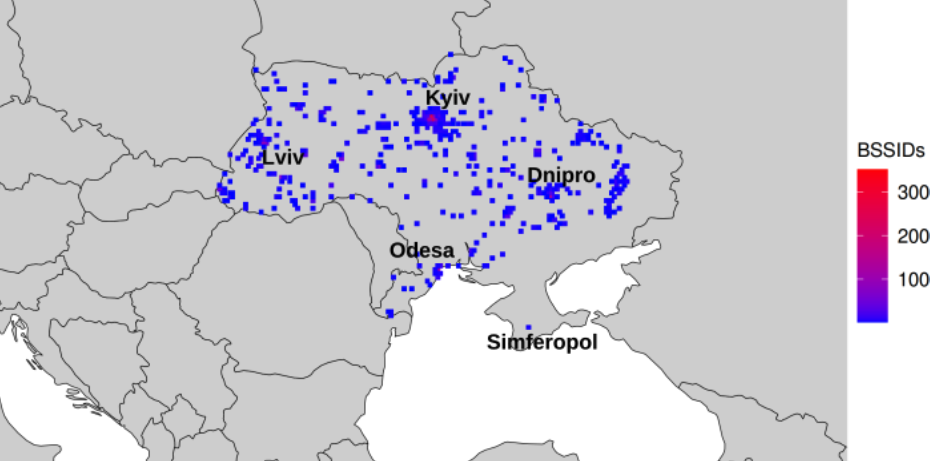
The researchers mentioned that by zeroing in on or “geofencing” different smaller areas listed by Apple’s location API, they may monitor how Wi-Fi entry factors moved over time. Why may that be an enormous deal? They discovered that by geofencing energetic battle zones in Ukraine, they had been capable of decide the placement and motion of Starlink units utilized by each Ukrainian and Russian forces.
The rationale they had been ready to do this is that every Starlink terminal — the dish and related {hardware} that permits a Starlink buyer to obtain Web service from a constellation of orbiting Starlink satellites — consists of its personal Wi-Fi entry level, whose location goes to be mechanically listed by any close by Apple units which have location companies enabled.
The College of Maryland group geo-fenced numerous battle zones in Ukraine, and recognized a minimum of 3,722 Starlink terminals geolocated in Ukraine.
“We discover what look like private units being introduced by navy personnel into conflict zones, exposing pre-deployment websites and navy positions,” the researchers wrote. “Our outcomes additionally present people who’ve left Ukraine to a variety of nations, validating public stories of the place Ukrainian refugees have resettled.”
In an interview with KrebsOnSecurity, the UMD group mentioned they discovered that along with exposing Russian troop pre-deployment websites, the placement information made it simple to see the place units in contested areas originated from.
“This consists of residential addresses all through the world,” Levin mentioned. “We even consider we are able to establish individuals who have joined the Ukraine Overseas Legion.”
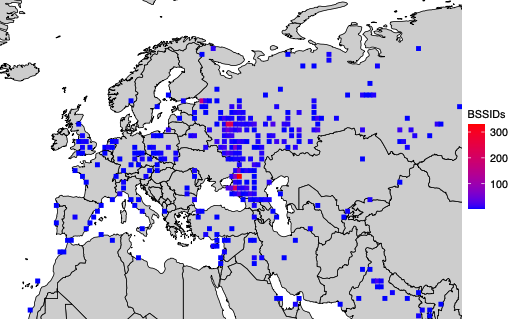
A simplified map of the place BSSIDs that enter the Donbas and Crimea areas of Ukraine originate. Picture: UMD.
Levin and Rye mentioned they shared their findings with Starlink in March 2024, and that Starlink advised them the corporate started transport software program updates in 2023 that pressure Starlink entry factors to randomize their BSSIDs.
Starlink’s father or mother SpaceX didn’t reply to requests for remark. However the researchers shared a graphic they mentioned was created from their Starlink BSSID monitoring information, which exhibits that simply prior to now month there was a considerable drop within the variety of Starlink units that had been geo-locatable utilizing Apple’s API.
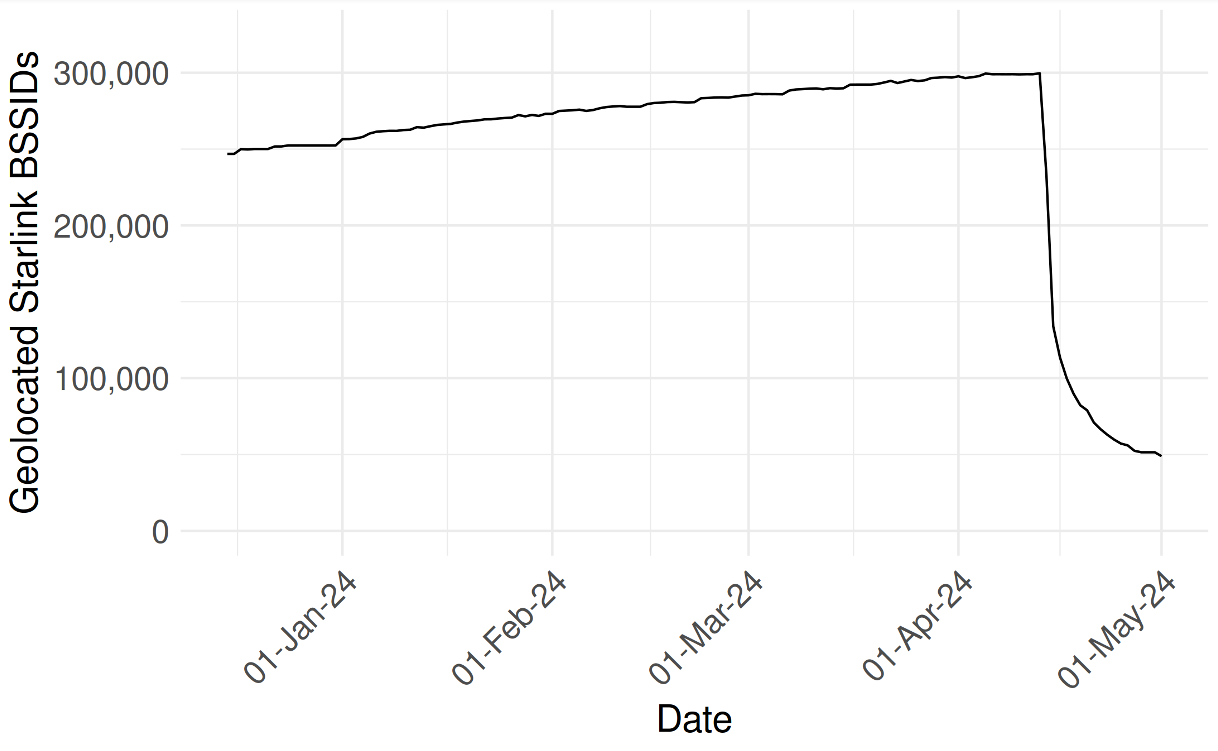
UMD researchers shared this graphic, which exhibits their skill to observe the placement and motion of Starlink units by BSSID dropped precipitously prior to now month.
In addition they shared a written assertion they obtained from Starlink, which acknowledged that Starlink Person Terminal routers initially used a static BSSID/MAC:
“In early 2023 a software program replace was launched that randomized the principle router BSSID. Subsequent software program releases have included randomization of the BSSID of WiFi repeaters related to the principle router. Software program updates that embrace the repeater randomization performance are at the moment being deployed fleet-wide on a region-by-region foundation. We consider the info outlined in your paper relies on Starlink fundamental routers and or repeaters that had been queried previous to receiving these randomization updates.”
The researchers additionally targeted their geofencing on the Israel-Hamas conflict in Gaza, and had been capable of monitor the migration and disappearance of units all through the Gaza Strip as Israeli forces minimize energy to the nation and bombing campaigns knocked out key infrastructure.
“As time progressed, the variety of Gazan BSSIDs which can be geolocatable continued to say no,” they wrote. “By the tip of the month, solely 28% of the unique BSSIDs had been nonetheless discovered within the Apple WPS.”
In late March 2024, Apple quietly up to date its web site to notice that anybody can choose out of getting the placement of their wi-fi entry factors collected and shared by Apple — by appending “_nomap” to the tip of the Wi-Fi entry level’s identify (SSID). Including “_nomap” to your Wi-Fi community identify additionally blocks Google from indexing its location.
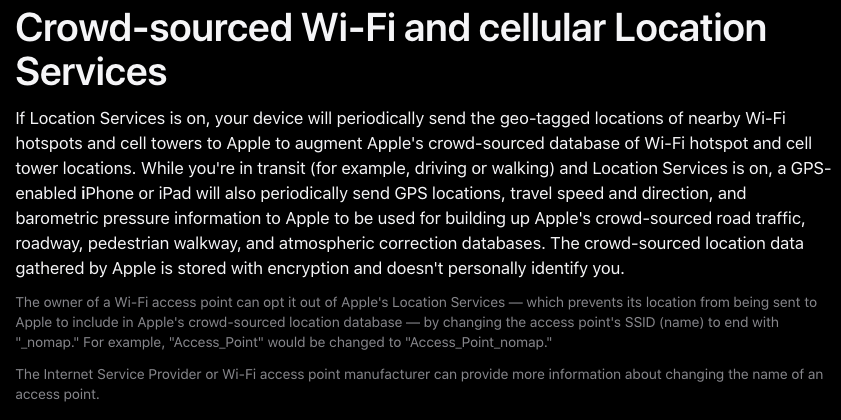
Apple up to date its privateness and site companies coverage in March 2024 to permit individuals to choose out of getting their Wi-Fi entry level listed by its service, by appending “_nomap” to the community’s identify.
Requested concerning the modifications, Apple mentioned they’ve revered the “_nomap” flag on SSIDs for a while, however that this was solely known as out in a assist article earlier this yr.
Rye mentioned Apple’s response addressed probably the most miserable side of their analysis: That there was beforehand no approach for anybody to choose out of this information assortment.
“You could not have Apple merchandise, however when you have an entry level and somebody close to you owns an Apple gadget, your BSSID will likely be in [Apple’s] database,” he mentioned. “What’s vital to notice right here is that each entry level is being tracked, with out opting in, whether or not they run an Apple gadget or not. Solely after we disclosed this to Apple have they added the power for individuals to choose out.”
The researchers mentioned they hope Apple will contemplate further safeguards, equivalent to proactive methods to restrict abuses of its location API.
“It’s a very good first step,” Levin mentioned of Apple’s privateness replace in March. “However this information represents a extremely severe privateness vulnerability. I’d hope Apple would put additional restrictions on the usage of its API, like rate-limiting these queries to maintain individuals from accumulating large quantities of knowledge like we did.”
The UMD researchers mentioned they omitted sure particulars from their examine to guard the customers they had been capable of monitor, noting that the strategies they used might current dangers for these fleeing abusive relationships or stalkers.
“We observe routers transfer between cities and nations, doubtlessly representing their proprietor’s relocation or a enterprise transaction between an outdated and new proprietor,” they wrote. “Whereas there’s not essentially a 1-to-1 relationship between Wi-Fi routers and customers, dwelling routers usually solely have a number of. If these customers are weak populations, equivalent to these fleeing intimate associate violence or a stalker, their router merely being on-line can disclose their new location.”
The researchers mentioned Wi-Fi entry factors that may be created utilizing a cellular gadget’s built-in mobile modem don’t create a location privateness threat for his or her customers as a result of cell phone hotspots will select a random BSSID when activated.
“Trendy Android and iOS units will select a random BSSID while you go into hotspot mode,” he mentioned. “Hotspots are already implementing the strongest suggestions for privateness protections. It’s different sorts of units that don’t try this.”
For instance, they found that sure generally used journey routers compound the potential privateness dangers.
“As a result of journey routers are steadily used on campers or boats, we see a big variety of them transfer between campgrounds, RV parks, and marinas,” the UMD duo wrote. “They’re utilized by vacationers who transfer between residential dwellings and motels. We have now proof of their use by navy members as they deploy from their houses and bases to conflict zones.”
A replica of the UMD analysis is obtainable right here (PDF).
Replace, Might 22, 4:54 p.m. ET: Added response from Apple.