
CISA warns of actively exploited Linux privilege elevation flaw

The U.S. Cybersecurity & Infrastructure Safety Company (CISA) has added two vulnerabilities in its Identified Exploited Vulnerabilities (KEV) catalog, together with a Linux kernel privilege elevation flaw.
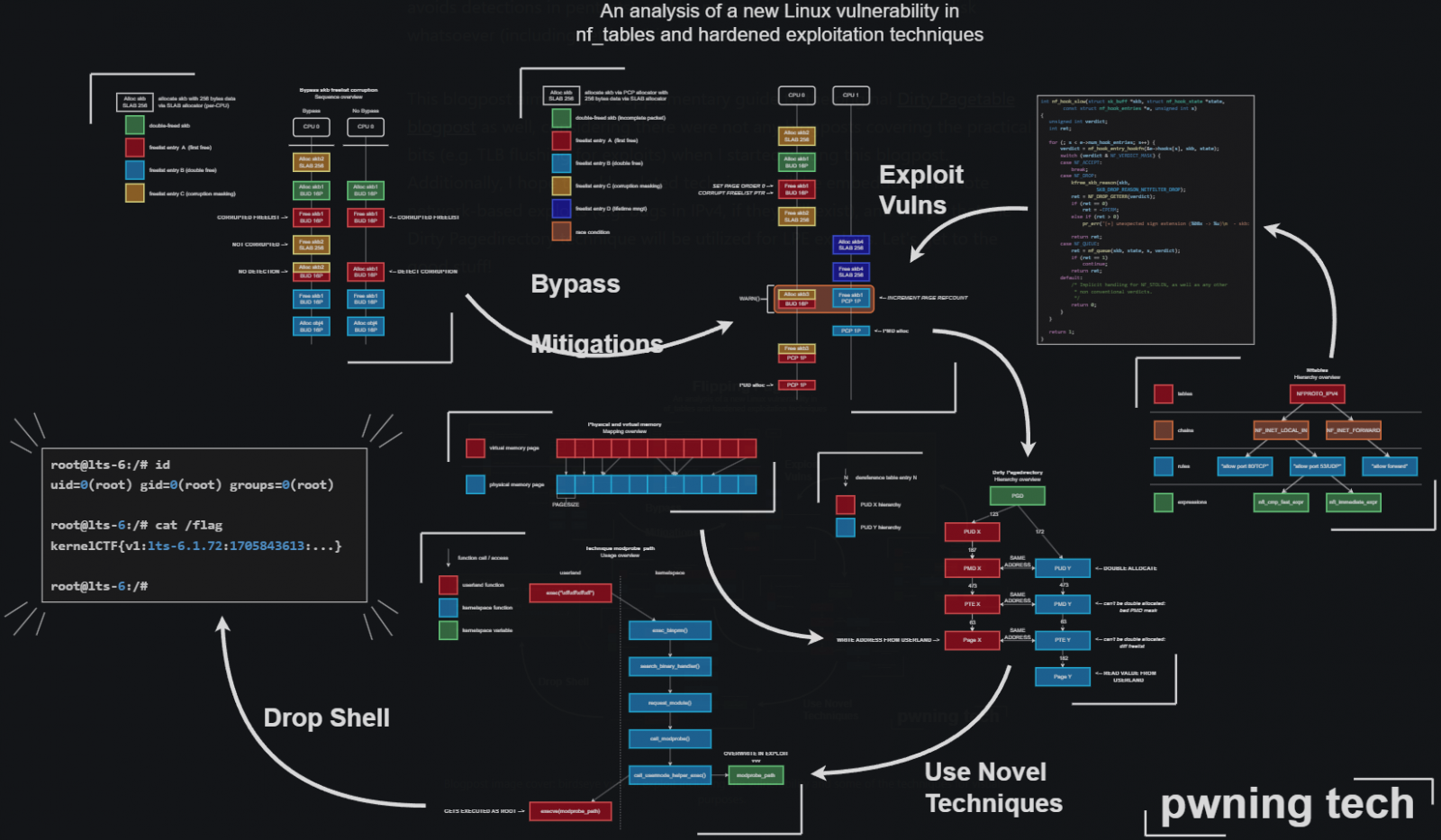
The high-severity flaw tracked as CVE-2024-1086 was first disclosed on January 31, 2024, as a use-after-free downside within the netfilter: nf_tables element, however was first launched by a commit in February 2014.
Netfilter is a framework supplied by the Linux kernel that permits numerous networking-related operations, comparable to packet filtering, community handle translation (NAT), and packet mangling.
The vulnerability is brought about as a result of the ‘nft_verdict_init()’ operate permits optimistic values for use as a drop error inside the hook verdict, inflicting the ‘nf_hook_slow()’ operate to execute a double free when NF_DROP is issued with a drop error that resembles NF_ACCEPT.
Exploitation of CVE-2024-1086 permits an attacker with native entry to realize privilege escalation on the goal system, probably gaining root-level entry.
The difficulty was mounted by way of a commit submitted in January 2024, which rejects QUEUE/DROP verdict parameters, thus stopping exploitation.
The repair has been backported to a number of secure kernel variations as listed beneath:
- v5.4.269 and later
- v5.10.210 and later
- v6.6.15 and later
- v4.19.307 and later
- v6.1.76 and later
- v5.15.149 and later
- v6.7.3 and later
In late March 2024, a safety researcher utilizing the alias ‘Notselwyn’ revealed a detailed write-up and proof-of-concept (PoC) exploit on GitHub, showcasing the best way to obtain native privilege escalation by exploiting the flaw on Linux kernel variations between 5.14 and 6.6.
Whereas most Linux distrobutions pushed out fixes pretty rapidly, Pink Hat had not pushed out a repair till March, making it potential that risk actors used the general public exploit on compromised methods.
CISA didn’t share particular particulars about how the vulnerability is exploited, however BleepingComputer has seen posts on hacking boards in regards to the public exploits.
The cybersecurity company has now given federal businesses till June 20, 2024, to use the out there patches.
If updating is just not potential, admins are advisable to use the next mitigations:
- Blocklist ‘nf_tables’ if it is not wanted/actively used.
- Prohibit entry to person namespaces to restrict the assault floor.
- Load the Linux Kernel Runtime Guard (LKRG) module (could cause instability)
The second flaw CISA added on the KEV catalog this time, additionally setting the due date to June 20, is CVE-2024-24919, an info disclosure vulnerability impacting VPN units from Examine Level.
Following the seller’s disclosure and safety replace launch for this flaw, researchers from Watchtowr Labs revealed their evaluation, underlining that the vulnerability is much worse than what Examine Level’s bulletin mirrored.




No Comment! Be the first one.