
The US Cybersecurity and Infrastructure Safety Company has added a essential safety bug in Linux to its listing of vulnerabilities recognized to be actively exploited within the wild.
The vulnerability, tracked as CVE-2024-1086 and carrying a severity ranking of seven.8 out of a attainable 10, permits individuals who have already gained a foothold inside an affected system to escalate their system privileges. It’s the results of a use-after-free error, a category of vulnerability that happens in software program written within the C and C++ languages when a course of continues to entry a reminiscence location after it has been freed or deallocated. Use-after-free vulnerabilities may end up in distant code or privilege escalation.
The vulnerability, which impacts Linux kernel variations 5.14 via 6.6, resides within the NF_tables, a kernel element enabling the Netfilter, which in flip facilitates quite a lot of community operations, together with packet filtering, community deal with [and port] translation (NA[P]T), packet logging, userspace packet queueing, and different packet mangling. It was patched in January, however because the CISA advisory signifies, some manufacturing techniques have but to put in it. On the time this Ars put up went dwell, there have been no recognized particulars concerning the energetic exploitation.
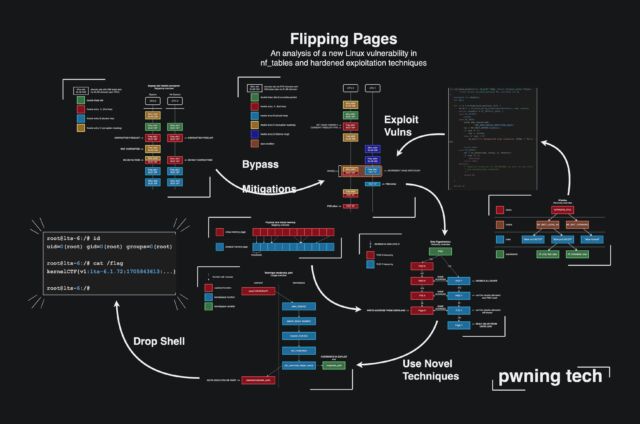
A deep-dive write-up of the vulnerability reveals that these exploits present “a really highly effective double-free primitive when the proper code paths are hit.” Double-free vulnerabilities are a subclass of use-after-free errors that happen when the free() operate for liberating reminiscence known as greater than as soon as for a similar location. The write-up lists a number of methods to use the vulnerability, together with code for doing so.
The double-free error is the results of a failure to attain enter sanitization in netfilter verdicts when nf_tables and unprivileged person namespaces are enabled. Among the handiest exploitation strategies permit for arbitrary code execution within the kernel and could be normal to drop a common root shell.
The writer supplied the next graphic offering a conceptual illustration:
CISA has given federal companies below its authority till June 20 to subject a patch. The company is urging all organizations which have but to use an replace to take action as quickly as attainable.
