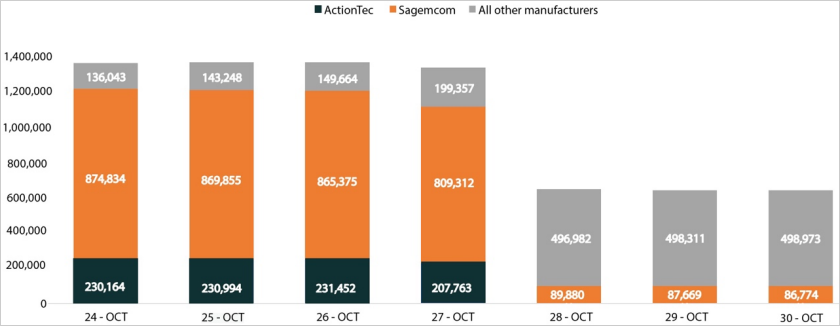
A malware botnet named ‘Pumpkin Eclipse’ carried out a mysterious damaging occasion in 2023 that destroyed 600,000 workplace/dwelling workplace (SOHO) web routers offline, disrupting clients’ web entry.
Based on researchers at Lumen’s Black Lotus Labs, who noticed the incident, it disrupted web entry throughout quite a few Midwest states between October 25 and October 27, 2023. This left house owners of the contaminated gadgets with no choice however to switch the routers.
Though large-scale, the incident had a targeted affect, affecting a single web service supplier (ISP) and three fashions of routers utilized by the agency: the ActionTec T3200s, ActionTec T3260s, and Sagemcom F5380.
Black Lotus Labs says the actual ISP serves weak communities in america and suffered a 49% discount in working modems as a result of ‘Pumpkin Eclipse’ incident.
Supply: Black Lotus Labs
Whereas Black Lotus didn’t identify the ISP, it bears a putting resemblance to a Windstream outage that occurred throughout the identical timeframe.
Beginning on October 25, 2023, Windstream clients started reporting on Reddit that their routers had been now not working.
“So I’ve had a T3200 modem for some time now, however at this time, one thing occurred that I’ve by no means skilled earlier than. The web mild is displaying stable crimson. What does it imply, and the way do I repair it?,” reported a person within the Winstream subreddit.
“Mine went down about 9PM final night time, ignored till I had time to troubleshoot this afternoon. After going by way of the chatbot (and the T3200 not responding to the manufacturing unit reset), it was fairly clear the router was the issue,” stated one other person.
Subscribers impacted by the Windstream outage had been instructed they wanted to switch the routers with a brand new one to revive their web entry.
When contacted concerning the incident, Windstream instructed BleepingComputer that they don’t have a remark.
Pumpkin Eclipse assault
Quick ahead seven months and a new report by Black Lotus could lastly shed some mild on the incident, explaining {that a} botnet was liable for bricking 600,000 routers throughout the midwest states at a single ISP in October 2023.
“Lumen Applied sciences’ Black Lotus Labs recognized a damaging occasion, as over 600,000 small workplace/dwelling workplace (SOHO) routers had been taken offline belonging to a single web service supplier (ISP). The incident came about over a 72-hour interval between October 25-27, rendered the contaminated gadgets completely inoperable, and required a hardware-based alternative. Public scan knowledge confirmed the sudden and precipitous elimination of 49% of all modems from the impacted ISP’s autonomous system quantity (ASN) throughout this time interval.”
❖ Black Lotus Labs
The researchers could not discover the vulnerability used for preliminary entry, so the attackers both used an unknown zero-day flaw or exploited weak credentials together with an uncovered administrative interface.
The primary stage payload is a bash script named “get_scrpc,” which executes to fetch a second script known as “get_strtriiush,” which is liable for retrieving and executing the first bot payload, ‘Chalubo’ (“mips.elf”).
Chalubo is executed from reminiscence to evade detection and makes use of ChaCha20 encryption when speaking with command and management (C2) servers to guard the communication channel, whereas it wipes all information from the disk and adjustments the method identify as soon as it is working.
The attacker can ship instructions to the bot by way of Lua scripts, which allow knowledge exfiltration, downloading of extra modules, or introducing new payloads on the contaminated gadget.
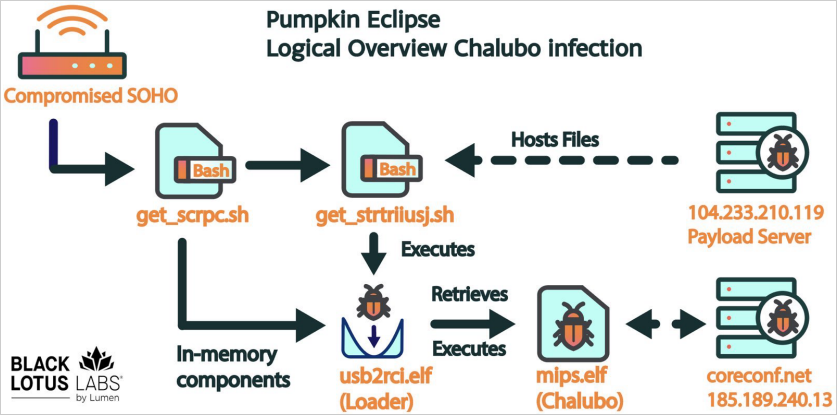
Supply: Black Lotus Labs
Upon execution, which features a 30-minute delay to evade sandboxes, the bot collects host-based info such because the MAC tackle, gadget ID, gadget sort, gadget model, and native IP tackle.
Chalubo has distributed denial of service (DDoS) performance, indicating Pumpkin Eclipse’s operational objectives. Nonetheless, Black Lotus Labs didn’t observe any DDoS assaults from the botnet.
The analysts be aware that Chalubo misses a persistence mechanism, so rebooting the contaminated router disrupts the bot’s operation.
Black Lotus Labs says its telemetry knowledge signifies that Chalubo operates 45 malware panels speaking over 650,000 distinctive IP addresses from October 3 to November 3, most primarily based in america.
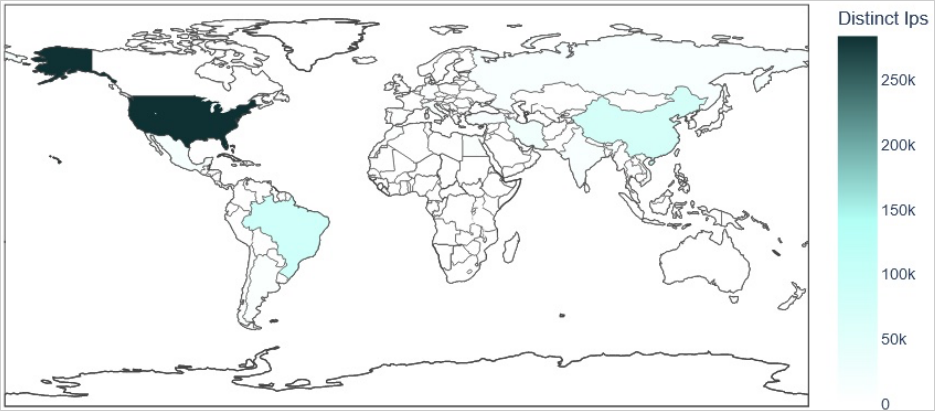
Supply: Black Lotus Labs
Solely considered one of these panels was used for the damaging assault and it targeted on a particular American ISP, inflicting Black Lotus researchers to imagine that the attacker bought the Chalubo panel for the particular function of deploying the damaging payload on routers.
“The second distinctive facet is that this marketing campaign was confined to a specific ASN. Most earlier campaigns we’ve seen goal a particular router mannequin or frequent vulnerability and have results throughout a number of suppliers’ networks. On this occasion, we noticed that each Sagemcom and ActionTec gadgets had been impacted on the similar time, each throughout the similar supplier’s community. This led us to evaluate it was not the results of a defective firmware replace by a single producer, which might usually be confined to at least one gadget mannequin or fashions from a given firm. Our evaluation of the Censys knowledge exhibits the affect was just for the 2 in query. This mix of things led us to conclude the occasion was possible a deliberate motion taken by an unattributed malicious cyber actor, even when we weren’t capable of get well the damaging module.” – Black Lotus
Sadly, the researchers couldn’t discover the payload used to brick the routers, in order that they had been unable to find out the way it was completed or for what function.
Black Lotus Labs notes that that is the primary time, aside from the “AcidRain” incident, {that a} botnet malware was ordered to destroy its hosts and trigger large-scale monetary harm by imposing {hardware} replacements.

